Within the last few months, a malvertiser has been pushing malicious tech support scam ads to users of Outlook, and other Microsoft owned apps in Windows 10. A cybersecurity study discovered that a Hong Kong-based hacker, known to operate the modus, has been part of a company called “fiber-ads.”
According to the report published by the cybersecurity firm, Confiant, penned by researcher Eliya Stein, the malvertiser is a Hong Kong citizen who operates as an intermediary. This means that those that “own the entire delivery chain, including the monetization after a victim, is infected,” the advertiser they discovered only distribute the scam ads.
“The middle-men provide the delivery mechanism, but from there the trail can get murky very quickly as the ultimate payload probably goes to the highest bidder, or to whomever the malvertiser is partnered with at that particular moment,” reads the Confiant report.
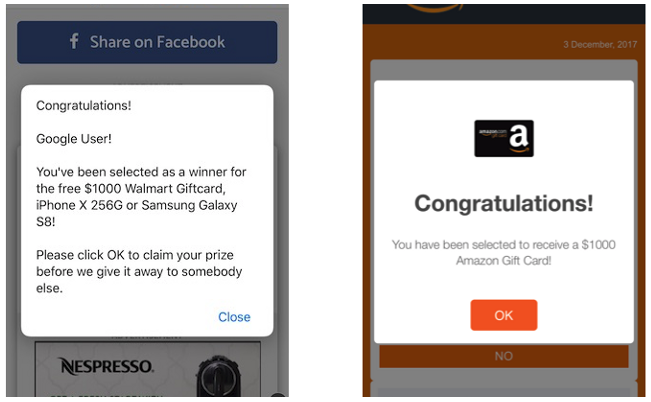
In order to do this, Confiant says that the malvertiser is using two companies to place ads in legitimate ad networks. These companies are named Fiber-Ads and Clockfollow. Much like other malicious ads, hidden codes are run through the ads delivered by the malvertiser and hijack those who view them, redirecting them to malicious, sometimes phishing, sites.
The hacker-malvertiser then use a popular ad-bidding platform called MyMediaAds in order to sell the malicious ads to other threat actors.
“While these incidents are somewhat unique in that they are spawned outside of the confines of a web browser, in-app advertisements are not the only vehicle of delivery for this particular attacker. In fact, this application-based activity is likely just spill over from this bad actor’s already active and disruptive malvertising rampage,” added Eliya Stein.
Read Complete Article: https://z6mag.com/2019/07/18/hong-kong-malvertiser-runs-malicious-tech-ads-in-microsoft-apps/