This is the first of monthly blog posts where we’ll provide a recap of ad security incidents for each month and which tier of SSPs and DSPs were impacted.
July was a very busy month for malvertising with redirect campaigns from familiar threat actors. Most notably, we observed consistent attacks every weekend for this month from both Nephos7 and eGobbler.
eGobbler and Nephos7 are two separate threat actors that Confiant separately tracks with our own specific tactics, techniques and procedures. However the two threat actors share a lot of commonalities, including their weekend attack pattern and the types of scams they push to their victims. For most of 2020, both groups had stayed away from the US and focused on Europe, but starting June 28, Confiant has blocked multiple campaigns targeting the US and shifting to a different type of payload based on "drive-by downloads" serving malware, and using fake software update imagery.
|
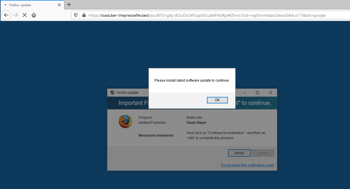
Example of carrier-branded scam as pushed by both eGobbler and Nephos7 in Europe |
|
Example of drive-by download as pushed by both eGobbler and Nephos7 in the US since June 28 and through July |
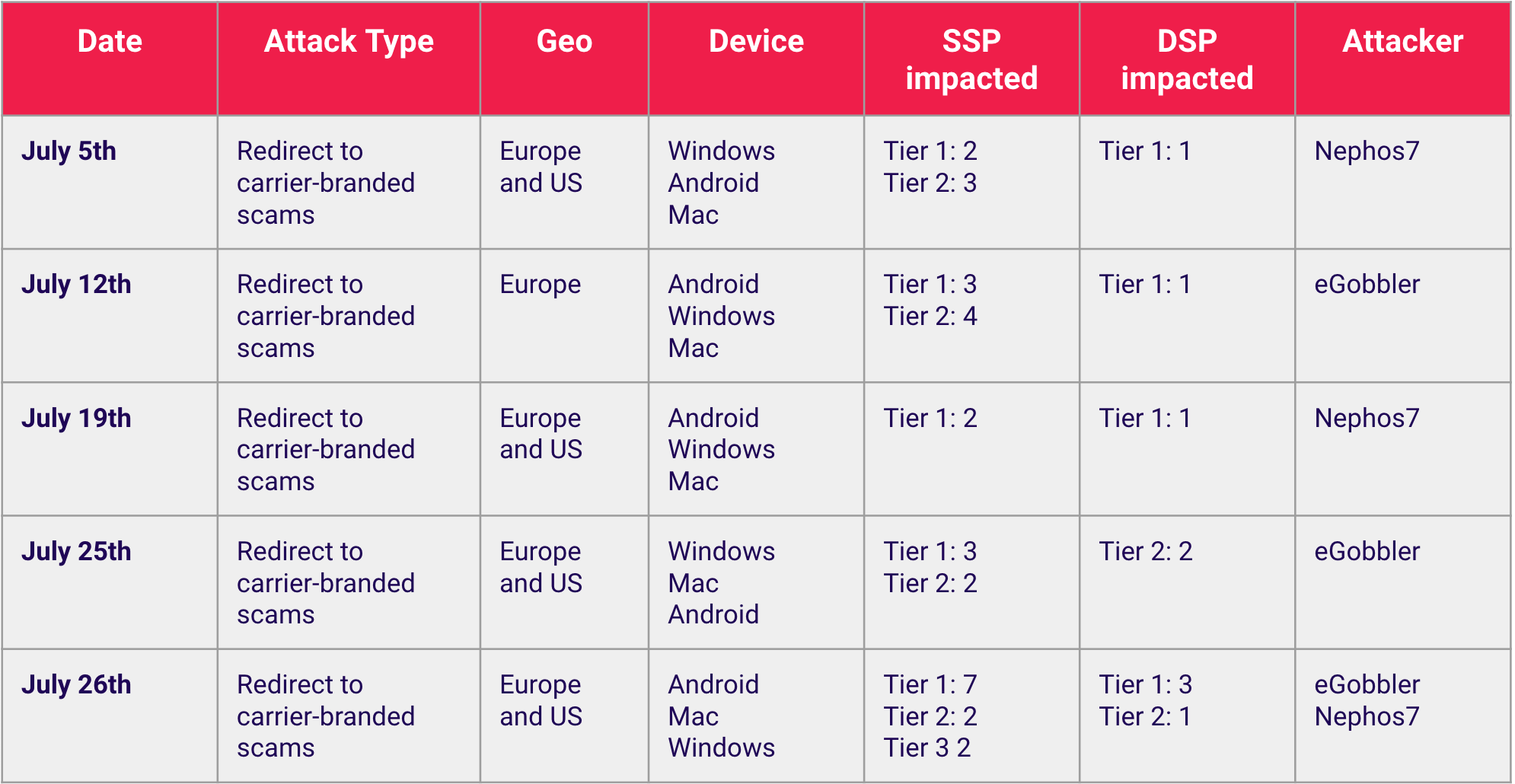
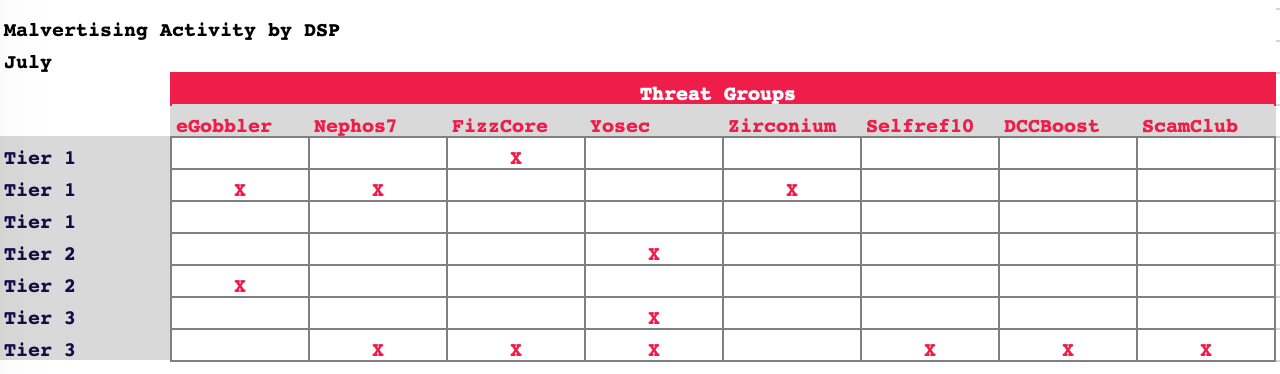
Here are some of the large attacks for July:
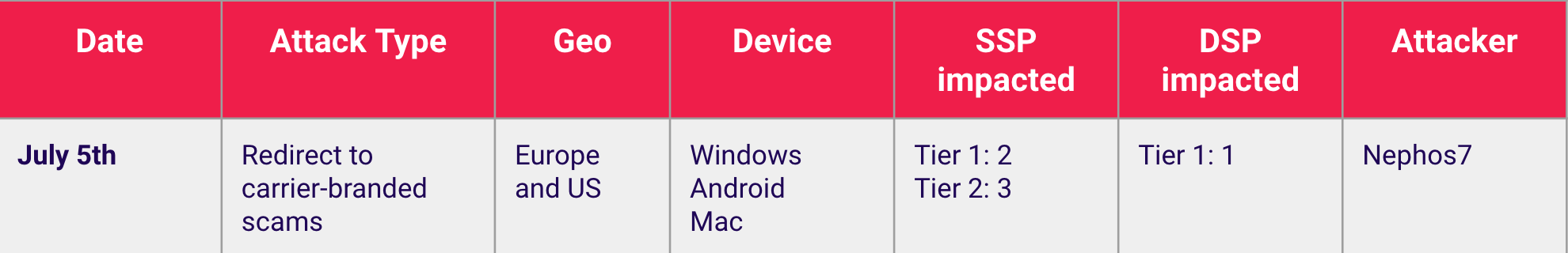
July 5th - Nephos7 targets EU with carrier-branded scams via tier 1 DSP. Germany was the biggest target, but Spain and France experienced significant volumes as well. Two tier 1 and three tier 2 SSPs.
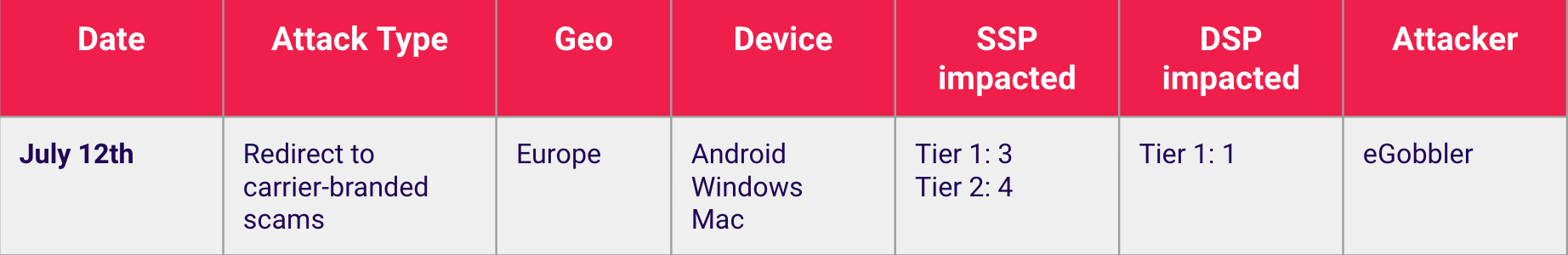
July 12th - eGobbler picks up where Nephos7 left off with a weekend wave of carrier-branded scams in EU again via tier 1 DSP. This time primarily targeting France. Thee tier 1 and four tier 2 SSPs were impacted.
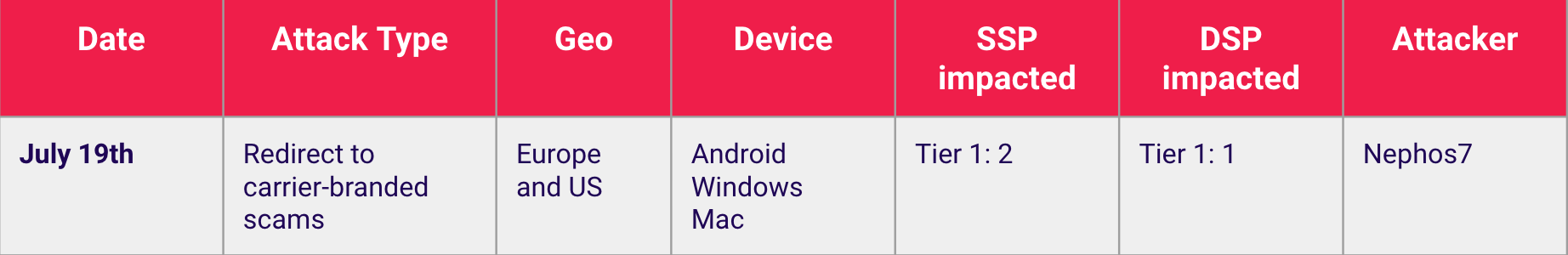
July 19th - eGobbler and Nephos7 continue to take turns. This weekend Nephos7 takes a round via tier 1 DSP, but expands targeting to include the United States with a significant portion of the campaign’s allocation. Two tier 1 SSPs were impacted.
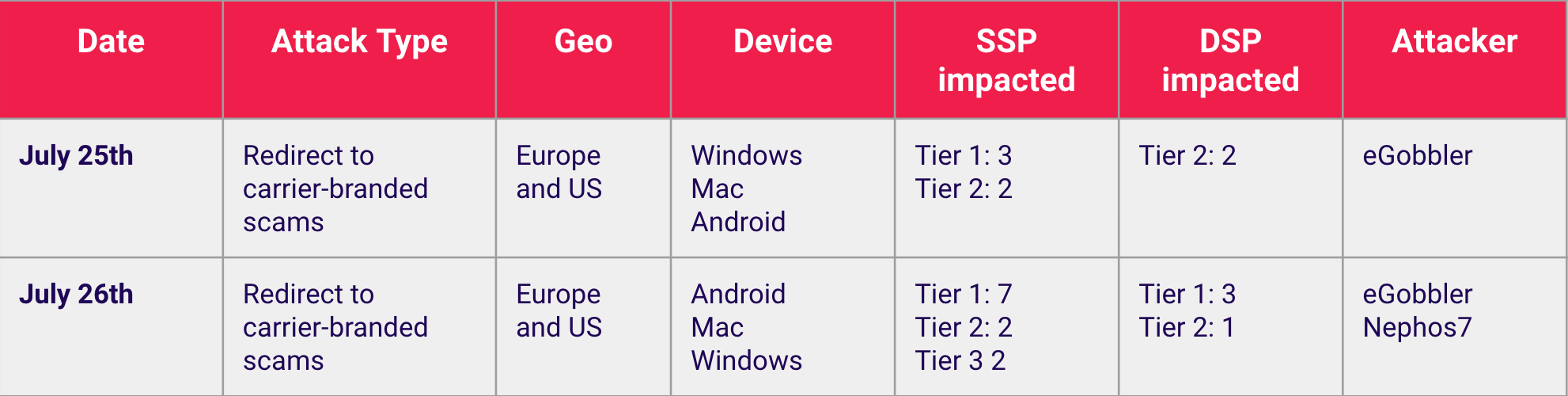
July 25th - 26th - eGobbler and Nephos7 both wreak havoc on ad tech with an expansion from carrier-branded scams to drive-by downloads on desktop devices. These happen via fake Flash or browser update landing pages and carry malware. Three tier 1 and one tier 2 DSPs were impacted.

-1.png?width=315&name=image%20(8)-1.png)